Is Your OT Infrastructure Cyber-Ready? Why Energy Leaders Are Rethinking Cybersecurity
Operational Technology (OT) environments across the energy sector are rapidly becoming interconnected with IT systems and cloud services. While this connectivity drives…
The Core Idea
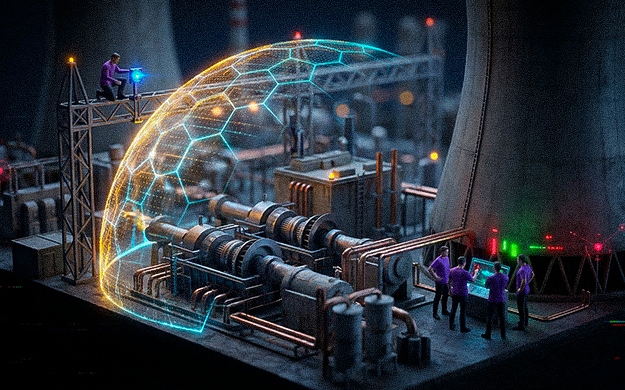
Operational Technology (OT) environments across the energy sector are rapidly becoming interconnected with IT systems and cloud services. While this connectivity drives efficiency, it also exposes critical infrastructure to cyber threats that traditional OT environments were never designed to handle.
Energy leaders are increasingly realizing that cyber resilience is no longer optional — OT networks must evolve to become cyber-ready.
Why This Matters
According to Fortinet’s 2025 Cybersecurity Readiness in the Energy Sector report:
- 78% of executives fear productivity loss due to cyberattacks
- 77% worry about direct revenue impact
- 68% report visibility gaps across OT environments
- 55% still operate legacy firmware across critical devices
In sectors where downtime translates directly into financial loss, regulatory exposure, and operational disruption, a single compromised endpoint can escalate into system-wide consequences.
OT systems that were once air-gapped are now connected to cloud dashboards, remote monitoring tools, and industrial IoT platforms — dramatically increasing the attack surface.
What Most Teams Get Wrong
- Assuming legacy OT systems remain secure simply because they were historically isolated
- Treating OT cybersecurity as an extension of IT security instead of a specialized domain
- Relying on perimeter defenses without implementing internal segmentation
- Delaying modernization due to operational risk concerns
These assumptions create a dangerous gap between perceived security and actual resilience.
A Smarter Way Forward
Effective OT cybersecurity requires a layered readiness framework built on three pillars:
1. Visibility & Segmentation
Every device must be identified and mapped — including legacy assets. Production networks must be segmented from corporate environments to prevent lateral movement.
2. Detection & Response
Industrial environments require monitoring solutions capable of analyzing industrial protocols such as Modbus, DNP3, and OPC. OT events should feed into centralized SOC/NOC environments for real-time correlation and response.
3. Resilience & Recovery
Organizations must assume compromise as a baseline scenario. Backup strategies should include offline storage, tested recovery procedures, and clearly defined response playbooks.
This framework shifts cybersecurity from reactive incident management to proactive infrastructure resilience.
Practical Actions
- Conduct a full OT asset visibility audit across all facilities
- Implement network segmentation between IT and OT systems
- Deploy monitoring solutions designed for industrial protocols
- Integrate OT environments into centralized SOC/NOC operations
- Establish tested incident response and recovery procedures
Closing Thought
Critical infrastructure is modernizing at an unprecedented pace. Connectivity is increasing, automation is expanding, and operational networks are becoming deeply integrated with digital systems.
Cyber resilience is no longer about preventing every attack — it is about ensuring that when disruptions occur, operations continue.
In the energy sector, preparedness is not just an IT priority. It is an operational necessity.
Want help implementing this?
Share your requirements. We'll recommend the right architecture, rollout approach, and governance model.
